Several social media platforms including Twitter and Discord are seeing a wave of phishing schemes to bait users into giving them their accounts. These scammers are threatening users with account abuse accusations and other scaring tactics.
Malwarebytes Labs, a cybersecurity platform, has found 2 phishing schemes like these in the past week. Social media platforms namely Twitter and Discord were targeted by these phishing schemes.
The Twitter phishing scam used Direct Message (DM) to trick users into giving them their login information. They first accused the user of breaking the terms of service and using hate speech. After that, they requested users to authenticate their accounts to stop their accounts from getting suspended. If you follow along, they redirect you to a fake help center where they ask the user for login information.
Discord phishing campaign messages users via their friends or any stranger’s account accusing them of breaking a server’s rule such as sending explicit images. This message contains a link to the server, and the user is required to log in using a QR code. According to MalwareBytes, if the user does this, their account will be taken over by scammers.
The CEO of SlashNext, Patrick Harr, warns users of such phishing attacks saying these are much smarter than traditional phishing scams. They use fear to make the victim move before he wonders if this is suspicious. These are said to be the most dangerous ones out of any social engineering scams.
Patrick Harr continues by saying that the scammers motivate Discord and Twitter users by threatening their business, status, or personal profile. This is what makes them so effective.
The main goal is to hijack the victim using psychological tactics and steal their bank accounts or other personal data. More importantly, getting access to an employee’s social media account gives access to information about the whole enterprise’s data and leaks a lot of information.
A security awareness advocate at KnowBe4, James McQuiggan says that a lot of times, phishing scams rely on the users’ emotions and create a sense of urgency and in a hurry, they make the wrong decisions. For example, in email phishing scams that rely on fear and urgency, users don’t bother checking the sender or link beforehand. This makes them susceptible to phishing attacks.
The same is the case with these Twitter and Discord scams that occurred last week. They threatened users with the possibility of their accounts being suspended or banned. This makes the user click on the link and open a fake website that looks exactly like the platform’s official login page.
Pressurizing victims into acting quickly and giving them their information before they notice anything suspicious seems to be the perfect strategy for these phishing scams. In the case of Twitter, the user would be taken aback considering the backlash from his account being suspended due to hate speech. This prevents them from noticing any red flags.
Phishing attacks are extremely dangerous to remote workers especially as they don’t have any interactions with their peers in person. This makes them highly reliant on social media platforms and digital workspaces.
Cybercriminals can easily check where and at what position a specific user works using Twitter or LinkedIn to target their scams.
Patrick Harr, says to counter these scams for online workspaces and remote workers, the organization should employ social engineering training as well as additional security measures.
Organizations should also implement mobile phishing protection for all personal and enterprise accounts.
Lastly, the fact of the matter is that phishing scams will never die down and instead get even better thanks to DeepFake technology. But such is the case with any new inventions, they have both good and bad sides.
Read next: PayPal becomes the new identity theft cover-up
by Arooj Ahmed via Digital Information World
"Mr Branding" is a blog based on RSS for everything related to website branding and website design, it collects its posts from many sites in order to facilitate the updating to the latest technology.
To suggest any source, please contact me: Taha.baba@consultant.com
Monday, July 18, 2022
WhatsApp Tests New Previews For Its Message Reactions Within Users’ Chat List
Popular texting platform WhatsApp may have been a little late in launching its reactions to messages, but the company is making sure the world knows how serious it is in terms of the theme.
We saw the feature be delivered to users on Telegram last year and in that regard, many hoped the launch of the app would come sooner than later. Even before that, it came time for Instagram to hop on the bandwagon of emojis being supported on its app too.
Now, we feel the wait may have been worth it as the company is taking the same theme to the next level. Developers from the tech giant are testing out new previews of reactions to messages. This recent expansion for different types of emojis is definitely something new as it’s the first time being down within a specific chat list.
We’ve got the news, fresh out of the oven thanks to WABetaInfo who claims many people are looking at it as a great change as a part of their chat overview.
Now, getting on the beta version surely does not guarantee a user regarding its availability as the update is a phased one. The new screenshots on the page showed how certain people or even group chats were being allotted a preview featuring the latest text reaction that came from their contact list.
It is strange to note how this functionality can’t be disabled, even if users work hard at switching the notifications off through their settings tab.
For now, the test is getting launched for a selected few beta testers but we do expect to see it expand further for all in the upcoming few weeks. But still, we’re not sure about the final release and hence will need to keep a lookout for that.
In case you happen to be a part of the exclusive WhatsApp beta group, you’ll be interested to know that you can check if you’ve received access to the interface.
Read next: WhatsApp Is Adding Quick Replies To Its PC App, And Is Testing Out New Time Limits For Deleting Messages Across iOS Platform
by Dr. Hura Anwar via Digital Information World
We saw the feature be delivered to users on Telegram last year and in that regard, many hoped the launch of the app would come sooner than later. Even before that, it came time for Instagram to hop on the bandwagon of emojis being supported on its app too.
Now, we feel the wait may have been worth it as the company is taking the same theme to the next level. Developers from the tech giant are testing out new previews of reactions to messages. This recent expansion for different types of emojis is definitely something new as it’s the first time being down within a specific chat list.
We’ve got the news, fresh out of the oven thanks to WABetaInfo who claims many people are looking at it as a great change as a part of their chat overview.
Now, getting on the beta version surely does not guarantee a user regarding its availability as the update is a phased one. The new screenshots on the page showed how certain people or even group chats were being allotted a preview featuring the latest text reaction that came from their contact list.
It is strange to note how this functionality can’t be disabled, even if users work hard at switching the notifications off through their settings tab.
For now, the test is getting launched for a selected few beta testers but we do expect to see it expand further for all in the upcoming few weeks. But still, we’re not sure about the final release and hence will need to keep a lookout for that.
In case you happen to be a part of the exclusive WhatsApp beta group, you’ll be interested to know that you can check if you’ve received access to the interface.
Read next: WhatsApp Is Adding Quick Replies To Its PC App, And Is Testing Out New Time Limits For Deleting Messages Across iOS Platform
by Dr. Hura Anwar via Digital Information World
Sunday, July 17, 2022
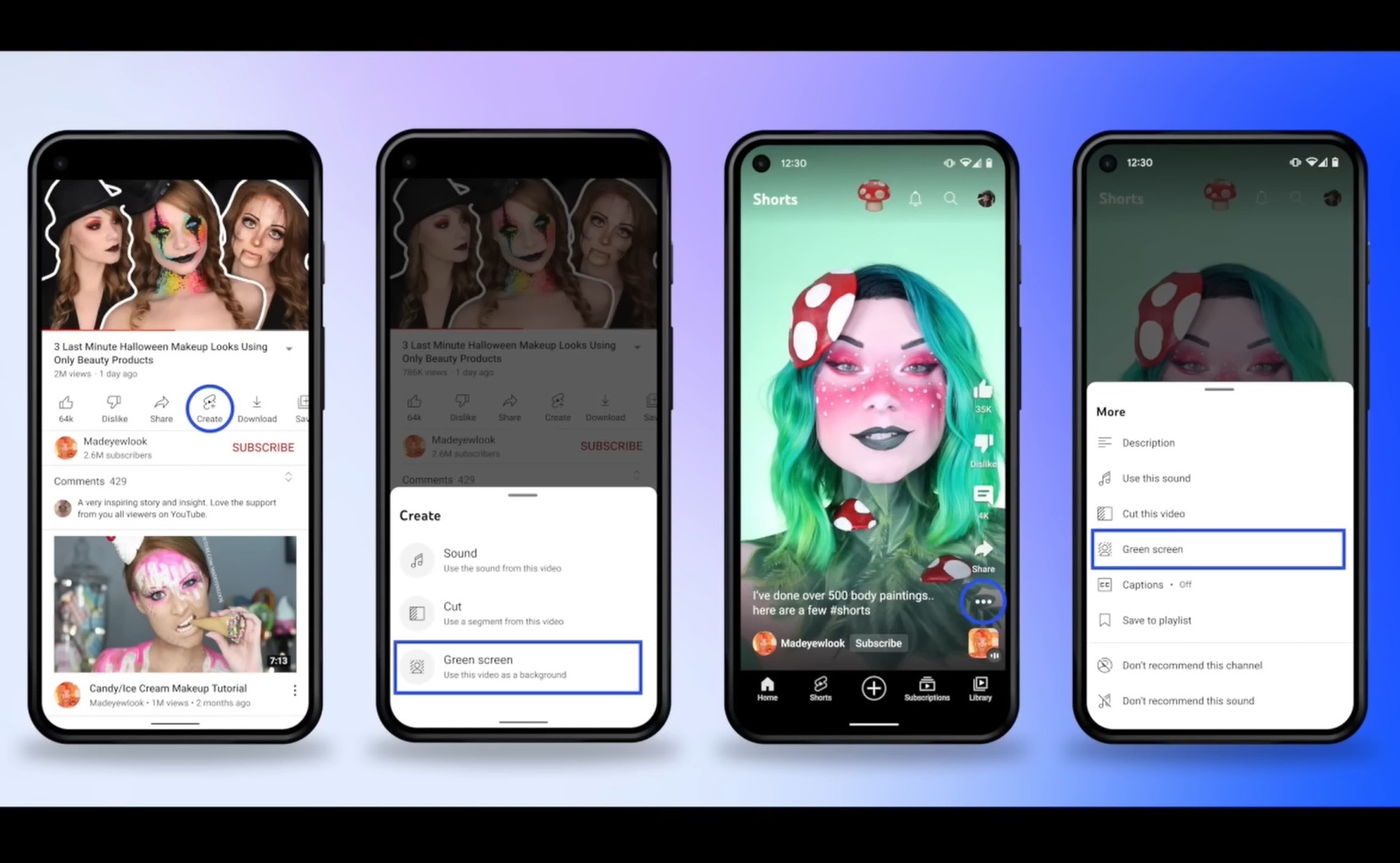
YouTube Provides Insights On New Shorts Features While Answering The Most Commonly Asked Creators Questions
YouTube is providing plenty of insight on a number of exciting features for its Shorts while answering the most frequently asked questions from audience members.
The leading social media giant is on its way toward the launch of two video remixing features that will soon be rolled out. These are titled Cut and Green Screen. But what’s important is to note how both of these features are in their early stages in terms of a launch for iOS users.
Cut feature gives users the ability to sample a one to five-second video from Shorts that are usually a part of many video beginnings. There are a number of ways by which users can enter and make the most of this feature.
For starters, click on the Create button and then you’ll find the Cut option pop up quickly. The second way is by entering the feature by taking a glance at the Shorts player. After witnessing the three-dot icon, you’ll find the Cut option.
But users need to note that if they do find someone creating a cut from any of their clips for a VOD or video on demand, users would immediately get a link for attribution for their video. And after you get it clicked, it guides a user back to a particular source video.
The second feature called the Green Screen is very new and it gives users the chance to sample around one minute of content present in a Short video clip or any other that can be found on the platform.
You can choose which type of content format you’d like to sample like audio or video and that is played against the background of your Short video.
Users are being given the chance to choose how much of the Short video they’d like to be prominent by simply pinching on the screen where your picture is being seen.
Just like the new Cut feature, if there is a person who samples your Green Screen video, there will be an attribution link provided that guides users back to the main source video.
Thanks to the analytics feature on the app, users would be given the chance to view the metrics related to any remixes that are made from a user’s video. But remember, there won’t be any differentiation provided to users about the audio, video, or even that related to Green Screen or Cut.
Next up, Shorts is introducing a new feature called Multiple Drafts. The whole goal is to provide users with the chance to save more than one draft in Shorts, provided you have one draft saved in the camera.
Hence, next time you have one saved, you’ll get the chance to have more. These are all affiliated to your device so if you alter your phone, you’ll lose it automatically.
Now, let’s take a look at some commonly asked questions by users answered on YouTube. Firstly, people asked if Shorts appear in the subscription feed and the answer is yes they do for all your subscribers.
People also wanted to know how many clips they’re allowed to import from a Shorts gallery and the answer is unlimited. But there is obviously a limit on duration which usually ends up being 60 seconds.
Is YouTube doing anything for Evergreen Shorts’ promotions? Well, the answer is yes it is. Also, YouTube says that if a person ends up using someone else’s shorts as a part of their video, the original creator always gets revenue for it.
Many creators also requested YouTube to make their Shorts video count toward the watching during public hours. The company hopes to work more on its Shorts funds and will be taking such feedback into consideration.
Lastly, should users add end screens in their Shorts? The app doesn’t recommend it as the views generated aren’t supported by the Shorts Player.
Read next: DeepMind Collaborates With YouTube On AI Research Models To Produce Auto-Generated Chapters For Videos
by Dr. Hura Anwar via Digital Information World
The leading social media giant is on its way toward the launch of two video remixing features that will soon be rolled out. These are titled Cut and Green Screen. But what’s important is to note how both of these features are in their early stages in terms of a launch for iOS users.
Cut feature gives users the ability to sample a one to five-second video from Shorts that are usually a part of many video beginnings. There are a number of ways by which users can enter and make the most of this feature.
For starters, click on the Create button and then you’ll find the Cut option pop up quickly. The second way is by entering the feature by taking a glance at the Shorts player. After witnessing the three-dot icon, you’ll find the Cut option.
But users need to note that if they do find someone creating a cut from any of their clips for a VOD or video on demand, users would immediately get a link for attribution for their video. And after you get it clicked, it guides a user back to a particular source video.
The second feature called the Green Screen is very new and it gives users the chance to sample around one minute of content present in a Short video clip or any other that can be found on the platform.
You can choose which type of content format you’d like to sample like audio or video and that is played against the background of your Short video.
Users are being given the chance to choose how much of the Short video they’d like to be prominent by simply pinching on the screen where your picture is being seen.
Just like the new Cut feature, if there is a person who samples your Green Screen video, there will be an attribution link provided that guides users back to the main source video.
Thanks to the analytics feature on the app, users would be given the chance to view the metrics related to any remixes that are made from a user’s video. But remember, there won’t be any differentiation provided to users about the audio, video, or even that related to Green Screen or Cut.
Next up, Shorts is introducing a new feature called Multiple Drafts. The whole goal is to provide users with the chance to save more than one draft in Shorts, provided you have one draft saved in the camera.
Hence, next time you have one saved, you’ll get the chance to have more. These are all affiliated to your device so if you alter your phone, you’ll lose it automatically.
Now, let’s take a look at some commonly asked questions by users answered on YouTube. Firstly, people asked if Shorts appear in the subscription feed and the answer is yes they do for all your subscribers.
People also wanted to know how many clips they’re allowed to import from a Shorts gallery and the answer is unlimited. But there is obviously a limit on duration which usually ends up being 60 seconds.
Is YouTube doing anything for Evergreen Shorts’ promotions? Well, the answer is yes it is. Also, YouTube says that if a person ends up using someone else’s shorts as a part of their video, the original creator always gets revenue for it.
Many creators also requested YouTube to make their Shorts video count toward the watching during public hours. The company hopes to work more on its Shorts funds and will be taking such feedback into consideration.
Lastly, should users add end screens in their Shorts? The app doesn’t recommend it as the views generated aren’t supported by the Shorts Player.
Read next: DeepMind Collaborates With YouTube On AI Research Models To Produce Auto-Generated Chapters For Videos
by Dr. Hura Anwar via Digital Information World
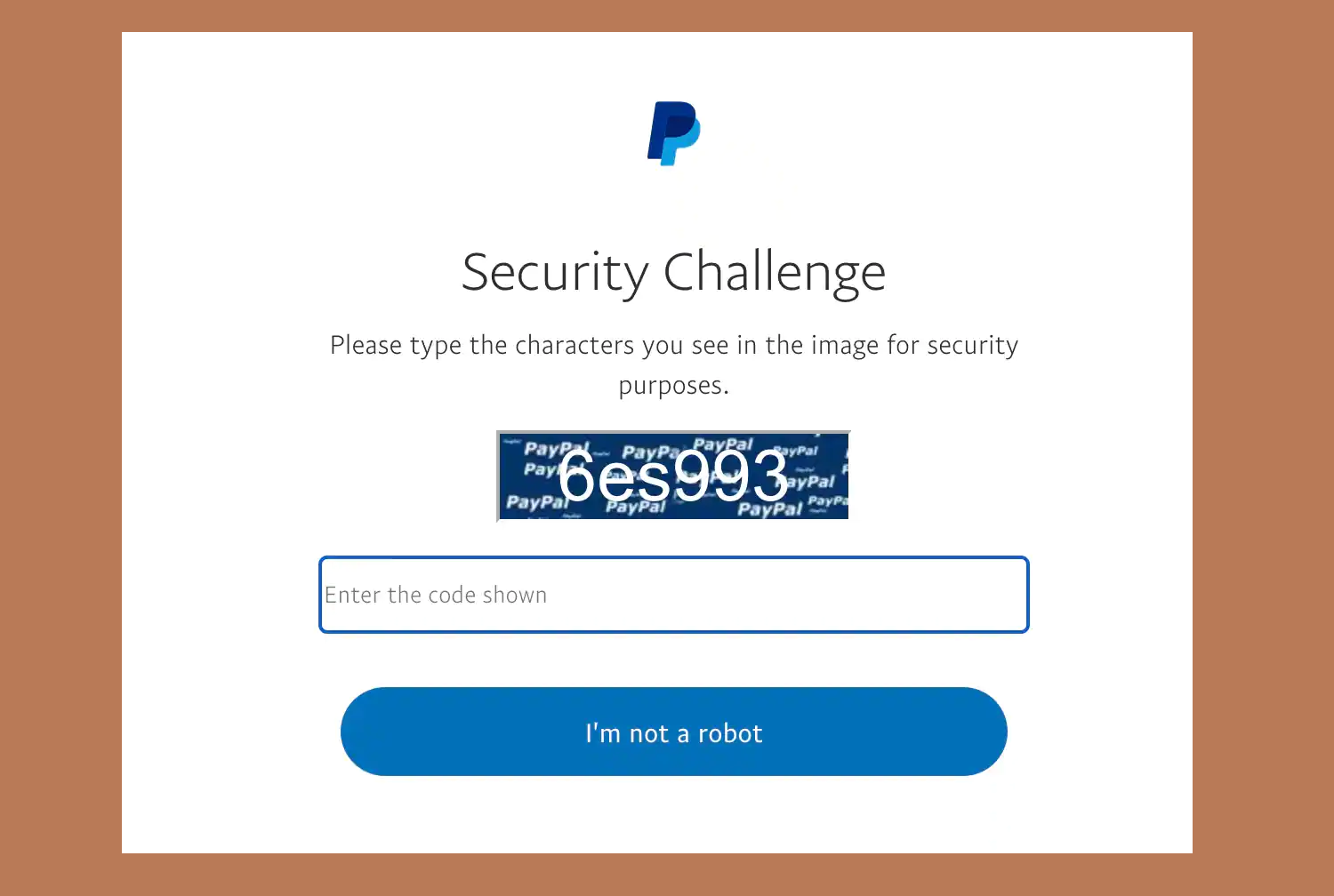
PayPal becomes the new identity theft cover-up
Identity thieves have found a new way to target and steal the identities of innocent victims through a trusted platform – PayPal, as reported by Akamai.
Voice phishing and misuse of information have been common for as long as the internet has existed. But did you know identity thefts are becoming equally common? This is quite alarming because a lot of fraud (money laundering, fake cryptocurrency accounts, etc.) can be committed by using someone else's identity and if it's done through the internet, there's little chance of accountability.
These malicious criminals have now developed a kit consisting of various pages that ask for personal information just like PayPal does. Since the design and logo are almost identical to that of the real app, there is little chance of not falling for the trap.
To give you a little more information about how the false PayPal works, we set out to test it for ourselves. You will first encounter a security challenge. A security challenge that works, and looks very similar to almost all other ones on authentic platforms.
Next, once the user has been 'confirmed', they are asked to enter their PayPal account information. Upon doing so, they are presented with a 'secure your account' warning, claiming that unusual activity has been spotted on their account. Since it is a platform concerning money, it is only natural that users comply immediately.
The personal information asked to 'secure' their accounts includes their credit card information, their ATM PIN, Social security number, name, date of birth, real address, and even their phone number. The faux setup even asks their mother's maiden name to make it look authentic. Email login credentials are also confirmed, along with a document that is issued by the government statement to submit a selfie as proof of identity.
When done with all of this, you will see a pop-up claiming that your identity has been confirmed and that your account is now secure.
The way this kit works is also almost fool-proof. Since it uses actual authentic WordPress sites to link itself to different users, one would hardly suspect it. The kit forces its way into WordPress sites by logging in through password-guessing or just forcing its way in.
The kit also cannot be identified by any security companies. The loophole here is that the kit has multiple checks on the connecting IP address. These are not identifiable by the security companies hence they cannot be discovered. As for URLs, the kit uses authentic URLs instead of the usual fake '.php' ones. This indicates that whoever is behind this has access and can generate real URLs.
But then how to know if you ever get attacked? Well, if you have been on PayPal for a long, you would know that it never asks for your ATM PIN. No platform would ever ask for your ATM PIN as a security measure. Furthermore, PayPal always asks for the password only once and never again. Lastly, the platform links credit card and bank details directly. Now that you know all this, it will lower your chances of getting phished.
Although we are at risk of getting phished too, we do have to appreciate the marvelous attempt here. Stay tuned to find out about any new upcoming phishing scams!
Read next: Vishing Scam Rates Are Getting Triple of Phishing Scams And Scammers are on the loose freely
by Arooj Ahmed via Digital Information World
Voice phishing and misuse of information have been common for as long as the internet has existed. But did you know identity thefts are becoming equally common? This is quite alarming because a lot of fraud (money laundering, fake cryptocurrency accounts, etc.) can be committed by using someone else's identity and if it's done through the internet, there's little chance of accountability.
These malicious criminals have now developed a kit consisting of various pages that ask for personal information just like PayPal does. Since the design and logo are almost identical to that of the real app, there is little chance of not falling for the trap.
To give you a little more information about how the false PayPal works, we set out to test it for ourselves. You will first encounter a security challenge. A security challenge that works, and looks very similar to almost all other ones on authentic platforms.
Next, once the user has been 'confirmed', they are asked to enter their PayPal account information. Upon doing so, they are presented with a 'secure your account' warning, claiming that unusual activity has been spotted on their account. Since it is a platform concerning money, it is only natural that users comply immediately.
The personal information asked to 'secure' their accounts includes their credit card information, their ATM PIN, Social security number, name, date of birth, real address, and even their phone number. The faux setup even asks their mother's maiden name to make it look authentic. Email login credentials are also confirmed, along with a document that is issued by the government statement to submit a selfie as proof of identity.
When done with all of this, you will see a pop-up claiming that your identity has been confirmed and that your account is now secure.
The way this kit works is also almost fool-proof. Since it uses actual authentic WordPress sites to link itself to different users, one would hardly suspect it. The kit forces its way into WordPress sites by logging in through password-guessing or just forcing its way in.
The kit also cannot be identified by any security companies. The loophole here is that the kit has multiple checks on the connecting IP address. These are not identifiable by the security companies hence they cannot be discovered. As for URLs, the kit uses authentic URLs instead of the usual fake '.php' ones. This indicates that whoever is behind this has access and can generate real URLs.
But then how to know if you ever get attacked? Well, if you have been on PayPal for a long, you would know that it never asks for your ATM PIN. No platform would ever ask for your ATM PIN as a security measure. Furthermore, PayPal always asks for the password only once and never again. Lastly, the platform links credit card and bank details directly. Now that you know all this, it will lower your chances of getting phished.
Although we are at risk of getting phished too, we do have to appreciate the marvelous attempt here. Stay tuned to find out about any new upcoming phishing scams!
Read next: Vishing Scam Rates Are Getting Triple of Phishing Scams And Scammers are on the loose freely
by Arooj Ahmed via Digital Information World
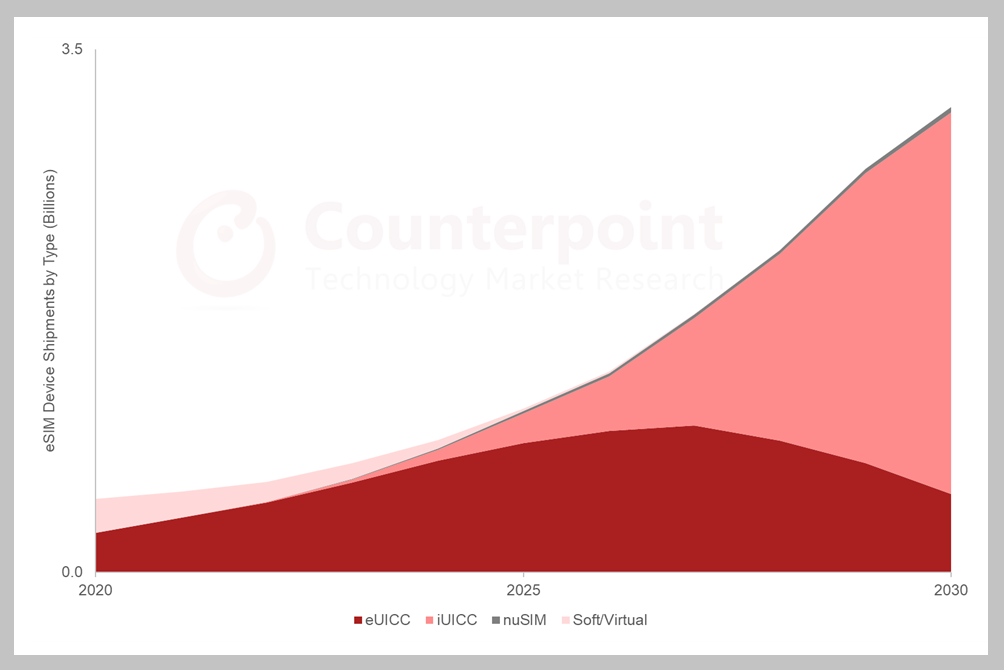
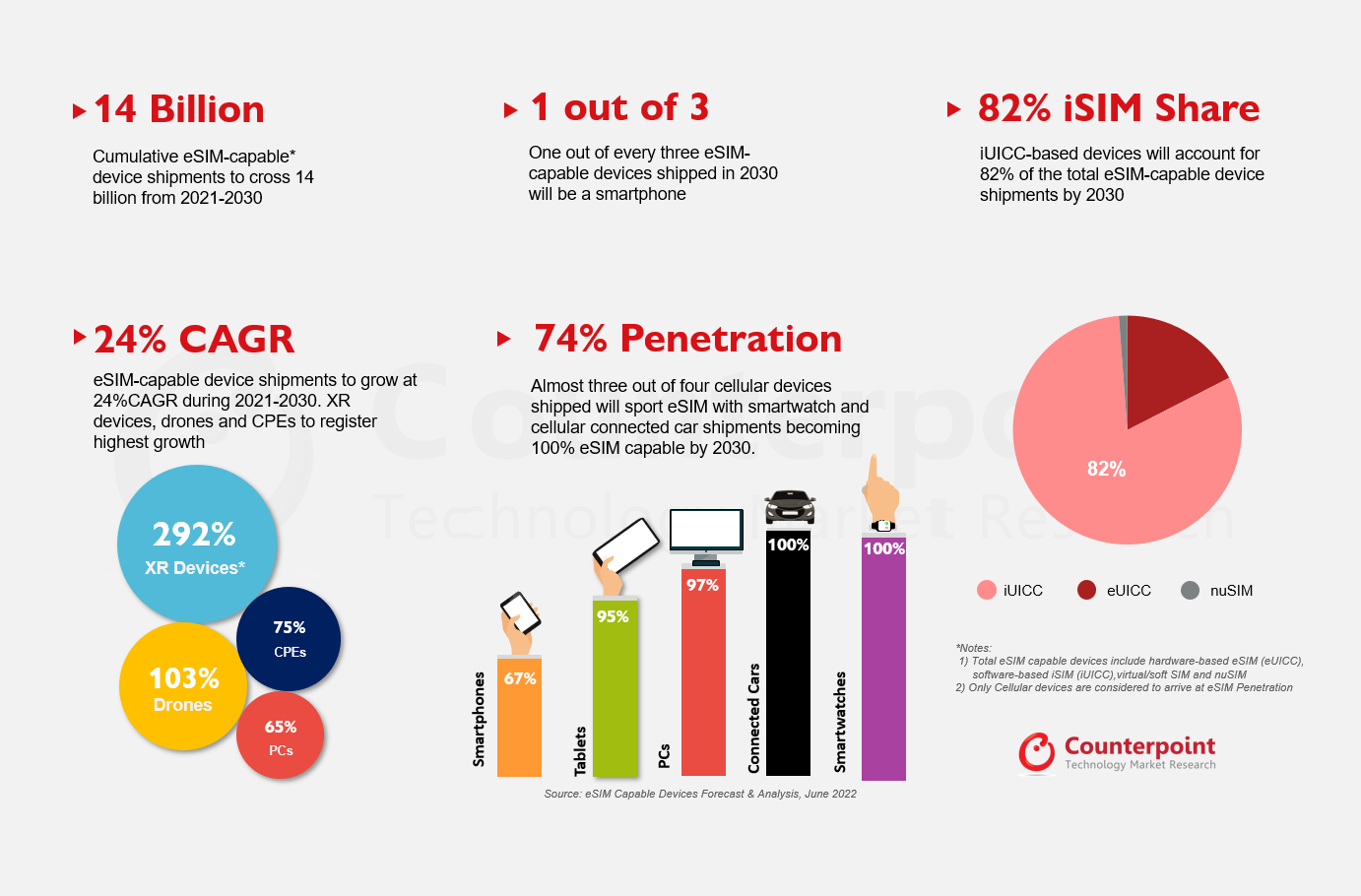
Shipments of iSIM-based cellular devices are going to cross 7 Billion in the next 8 years
eSIM devices are very popular now and approximately 14 million will be shipped from 2021 to 2030. These eSIM devices include all kinds including eSIM, iSIM, nuSIM, and SoftSIM.
Why is the device so popular? Since it is an updated technology, has ample flexibility, is cost-efficient, is highly safe, and has numerous other benefits, it is seen to be a highly popular item. The passing year has shown proof of the popularity of this technology by surpassing a shipment of around 350 million hardware eSIM devices.
For the next 5 years, it is predicted that eSIM hardware devices will have a better hold of the industry. These include smartphones, smartwatches, tablets, etc. These are said to make up half of the shipment by 2027. This year, it is predicted that the item version will be much more in-demand.
Researchers and experts have commented how eSIMs have always been the best out of all the others. They have been well received by the users as compared to nurses or SoftSims. However, items are here to break that record. iSIM chips have been much more popular than the physical MFF2/WLCSP chips within a year of their launch and are predicted to take over the market this year.
The iSIM will first be adopted by major platforms supporting IoT chipsets and modules. Nokia, Apple, Samsung, and all bug names in the industry will harbor this new technology. iSIM shipments alone are said to score 7 billion from 2021 to 2030 alone.
Research analysts confirm that there will be an evident change in the upcoming years in terms of eSIM-capable devices. Where there is the launch of an iPhone consisting of the eSIM only, it can be anticipated that the technology will shift to iSIM only as well in a few years.
While the eSIM can be used across various devices, including smartphones, laptops, watches, and such devices, only one is said to be the most popular. Smartphones are going to be the most popular devices with eSIMs and will be a huge economic relief to all companies. Since traditional SIMs are very complex to operate and not friendly to produce economically, eSIMs are already preferred.
In the coming years, we will have to see if eSIMs are actually the future or will iSIMs take over.
H/T: Counterpointresearch
Read next: Vishing Scam Rates Are Getting Triple of Phishing Scams And Scammers are on the loose freely
by Arooj Ahmed via Digital Information World
Why is the device so popular? Since it is an updated technology, has ample flexibility, is cost-efficient, is highly safe, and has numerous other benefits, it is seen to be a highly popular item. The passing year has shown proof of the popularity of this technology by surpassing a shipment of around 350 million hardware eSIM devices.
For the next 5 years, it is predicted that eSIM hardware devices will have a better hold of the industry. These include smartphones, smartwatches, tablets, etc. These are said to make up half of the shipment by 2027. This year, it is predicted that the item version will be much more in-demand.
Researchers and experts have commented how eSIMs have always been the best out of all the others. They have been well received by the users as compared to nurses or SoftSims. However, items are here to break that record. iSIM chips have been much more popular than the physical MFF2/WLCSP chips within a year of their launch and are predicted to take over the market this year.
The iSIM will first be adopted by major platforms supporting IoT chipsets and modules. Nokia, Apple, Samsung, and all bug names in the industry will harbor this new technology. iSIM shipments alone are said to score 7 billion from 2021 to 2030 alone.
Research analysts confirm that there will be an evident change in the upcoming years in terms of eSIM-capable devices. Where there is the launch of an iPhone consisting of the eSIM only, it can be anticipated that the technology will shift to iSIM only as well in a few years.
While the eSIM can be used across various devices, including smartphones, laptops, watches, and such devices, only one is said to be the most popular. Smartphones are going to be the most popular devices with eSIMs and will be a huge economic relief to all companies. Since traditional SIMs are very complex to operate and not friendly to produce economically, eSIMs are already preferred.
In the coming years, we will have to see if eSIMs are actually the future or will iSIMs take over.
H/T: Counterpointresearch
Read next: Vishing Scam Rates Are Getting Triple of Phishing Scams And Scammers are on the loose freely
by Arooj Ahmed via Digital Information World
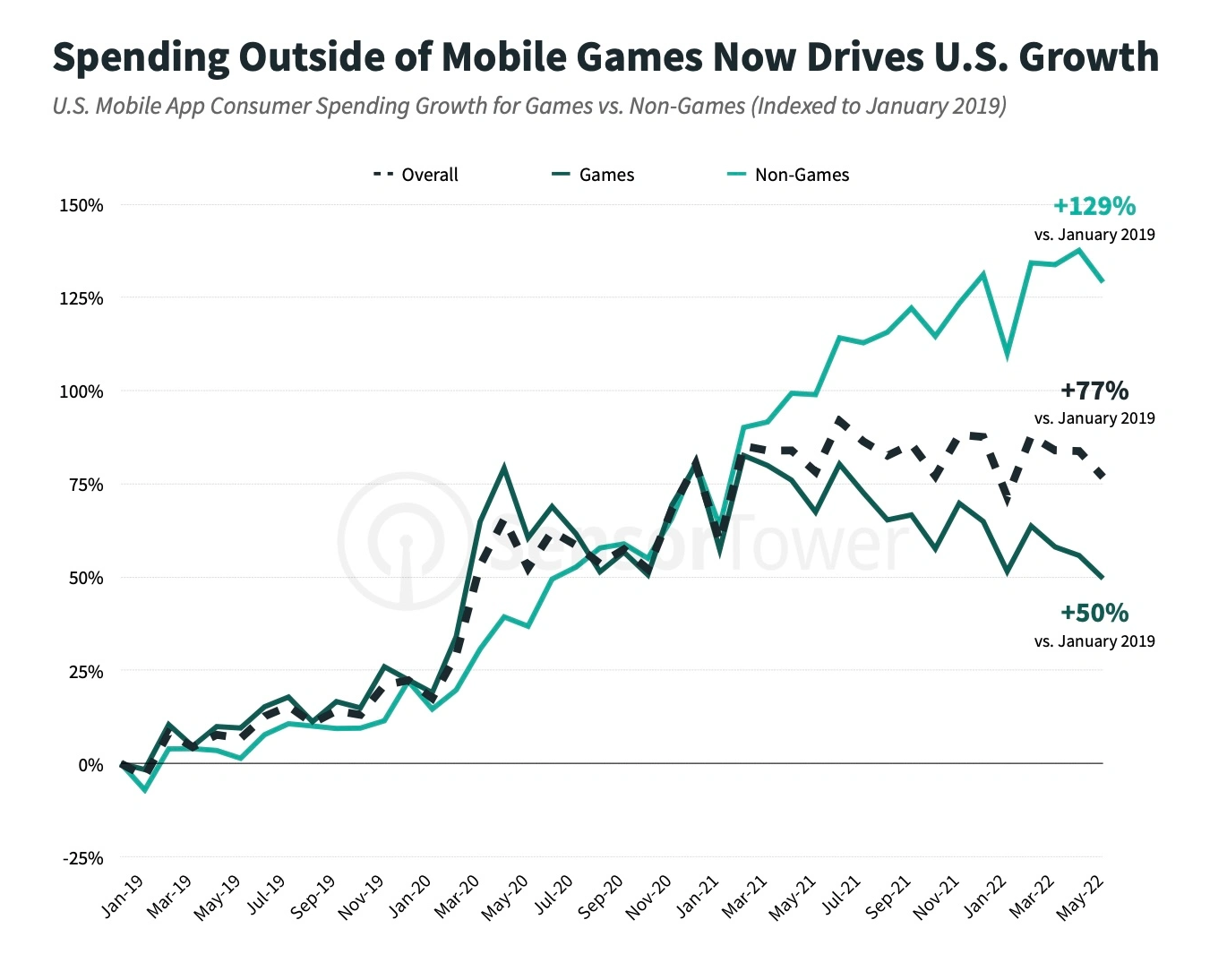
Revenue For Non-Games Just Topped Games In The App Store For The Very First Time In US
Data shows that non-gaming apps in the app store topped games apps in the US for the very first time and it is surprising, to say the least. This got reported in May 2022 but it didn't stop there because the revenue for non-games continued topping gaming apps in June 2022. So the total revenue generated in the first quarter of the year was about $3.4 billion as compared to the $3.3 billion of games in the U.S App Store.
This new development was only seen in the U.S App Store but Google Play Store still has games in the top ranks, followed by non-game apps. After May, as per Sensor Tower’s Q2 2022 Data Digest, about 50.3% of the earnings were directly coming from non-games in June in the U.S. If we do the comparison, we find out that games covered one-third of the whole earnings of the U.S App Store about five years ago. The difference is huge and there are a lot of factors that contributed to this. This shift tells how the U.S Apple Store has succeeded to broaden the economy by adding different types of apps to their App Store so that they can generate larger revenues.
If we talk about the past revenues, in 2019 and 2020 the earnings for games apps were at an all-time high. But after covid, the change could be seen clearly because the non-games app exceeded games with a huge difference. But this still is not good news because as the number of non-games apps has gotten higher, there is still a chance that games will dominate them after the covid surge. Reports are saying that in Q2, games can again take their place and non-game apps will be left behind. But saying anything before the time comes is foolish.
The most downloaded non-game this quarter half of the year was TikTok and it has been in the top 8 times out of ten these past quarters. It brought about 187 million revenues into the market. Then it was followed by Instagram, Facebook, WhatsApp, and Snapchat. The top mobile game downloaded was Subway Surfers and the second highest download game was Garena Free Fire. Subway Surfer got 80 Million downloads while Free Fire got 70 million downloads this half of the year.
Read next: Gen Z is all set to become the educated generation in their pursuit of a happy life
by Arooj Ahmed via Digital Information World
This new development was only seen in the U.S App Store but Google Play Store still has games in the top ranks, followed by non-game apps. After May, as per Sensor Tower’s Q2 2022 Data Digest, about 50.3% of the earnings were directly coming from non-games in June in the U.S. If we do the comparison, we find out that games covered one-third of the whole earnings of the U.S App Store about five years ago. The difference is huge and there are a lot of factors that contributed to this. This shift tells how the U.S Apple Store has succeeded to broaden the economy by adding different types of apps to their App Store so that they can generate larger revenues.
If we talk about the past revenues, in 2019 and 2020 the earnings for games apps were at an all-time high. But after covid, the change could be seen clearly because the non-games app exceeded games with a huge difference. But this still is not good news because as the number of non-games apps has gotten higher, there is still a chance that games will dominate them after the covid surge. Reports are saying that in Q2, games can again take their place and non-game apps will be left behind. But saying anything before the time comes is foolish.
The most downloaded non-game this quarter half of the year was TikTok and it has been in the top 8 times out of ten these past quarters. It brought about 187 million revenues into the market. Then it was followed by Instagram, Facebook, WhatsApp, and Snapchat. The top mobile game downloaded was Subway Surfers and the second highest download game was Garena Free Fire. Subway Surfer got 80 Million downloads while Free Fire got 70 million downloads this half of the year.
Read next: Gen Z is all set to become the educated generation in their pursuit of a happy life
by Arooj Ahmed via Digital Information World
A cyber threat to the users’ data on Google’s search engine is leaking private information
Since May 2020, a continuous malware campaign has been roaming around the corner and affecting multiple browsers, including Microsoft Edge, Mozilla Firefox, Google Chrome, etc. Before jumping to the biggest threat to the users’ data due to an adware campaign, one must know what adware is? Adware is a programming application in which threat actors can display advertisements, or when a person opens up a website, ads are shown through pop-up windows or adverts displayed on the UI.
It is essential to mention here that a network security analyst, Palo Alto, recognized adware designed to target search domain requests using a malware browser extension to launch its payload. The malware, Dubbed ChromeLoader, is an extremely dangerous and pervasive browser hijacker. It uses simple malicious ads, redirects user traffic to advertisement sites, and harms organizations by stealing their confidential information, modifying the browser’s settings, and leaking it publically. The kind of malware exposed by Alto operates by a browser extension and appears to reveal the stolen search engine history. This malware also serves as both an information stealer and adware. This way, it is deployed to fetch the public’s search data without asking for their permission.
The question is, how does this malware work? In simple words, the extension installs a listener, blocks every outgoing request, and verifies the request sent to Yahoo, DuckDuckGo, or Google search engine. When it crosschecks the sent requests, the extension will automatically transfer the user’s search data to the C2 (it is the cyberattackers’ control servers to receive commands). Cybercriminals now have all the data and access to victims’ interests and preferences. On July 12, the existence of this adware campaign was finally revealed to the public, though this suspicious malware activity started at the start of 2022. During this time, the software has undergone several changes. Threat actors modify software coding from time to time to make it more malicious. Alto Palo thinks it will get refined more, and the process seems to continue.
Explaining further about ChromeLoader, Palo said that it is multi-stage malware consisting of multiple stages throughout its attacking chain. He identified four variants of ChromeLoader. Three were designed to attack Windows systems, and a fourth variant targeted the Mac operating system. Additionally, the malware creators used confusing techniques to hide their tracks. In the case of search engine stealing, they used a special coding called switch-case-oriented programming that allows cybercriminals to make it way harder for IT experts to detect.
It is necessary to detect and reduce these types of threats. The companies must provide additional security features to protect users from data breaches. It is also essential for enterprises to understand the malicious behaviors and give tools to encounter these cyber threats.
Read next: Vishing Scam Rates Are Getting Triple of Phishing Scams And Scammers are on the loose freely
by Arooj Ahmed via Digital Information World
It is essential to mention here that a network security analyst, Palo Alto, recognized adware designed to target search domain requests using a malware browser extension to launch its payload. The malware, Dubbed ChromeLoader, is an extremely dangerous and pervasive browser hijacker. It uses simple malicious ads, redirects user traffic to advertisement sites, and harms organizations by stealing their confidential information, modifying the browser’s settings, and leaking it publically. The kind of malware exposed by Alto operates by a browser extension and appears to reveal the stolen search engine history. This malware also serves as both an information stealer and adware. This way, it is deployed to fetch the public’s search data without asking for their permission.
The question is, how does this malware work? In simple words, the extension installs a listener, blocks every outgoing request, and verifies the request sent to Yahoo, DuckDuckGo, or Google search engine. When it crosschecks the sent requests, the extension will automatically transfer the user’s search data to the C2 (it is the cyberattackers’ control servers to receive commands). Cybercriminals now have all the data and access to victims’ interests and preferences. On July 12, the existence of this adware campaign was finally revealed to the public, though this suspicious malware activity started at the start of 2022. During this time, the software has undergone several changes. Threat actors modify software coding from time to time to make it more malicious. Alto Palo thinks it will get refined more, and the process seems to continue.
Explaining further about ChromeLoader, Palo said that it is multi-stage malware consisting of multiple stages throughout its attacking chain. He identified four variants of ChromeLoader. Three were designed to attack Windows systems, and a fourth variant targeted the Mac operating system. Additionally, the malware creators used confusing techniques to hide their tracks. In the case of search engine stealing, they used a special coding called switch-case-oriented programming that allows cybercriminals to make it way harder for IT experts to detect.
It is necessary to detect and reduce these types of threats. The companies must provide additional security features to protect users from data breaches. It is also essential for enterprises to understand the malicious behaviors and give tools to encounter these cyber threats.
Read next: Vishing Scam Rates Are Getting Triple of Phishing Scams And Scammers are on the loose freely
by Arooj Ahmed via Digital Information World
Subscribe to:
Posts (Atom)