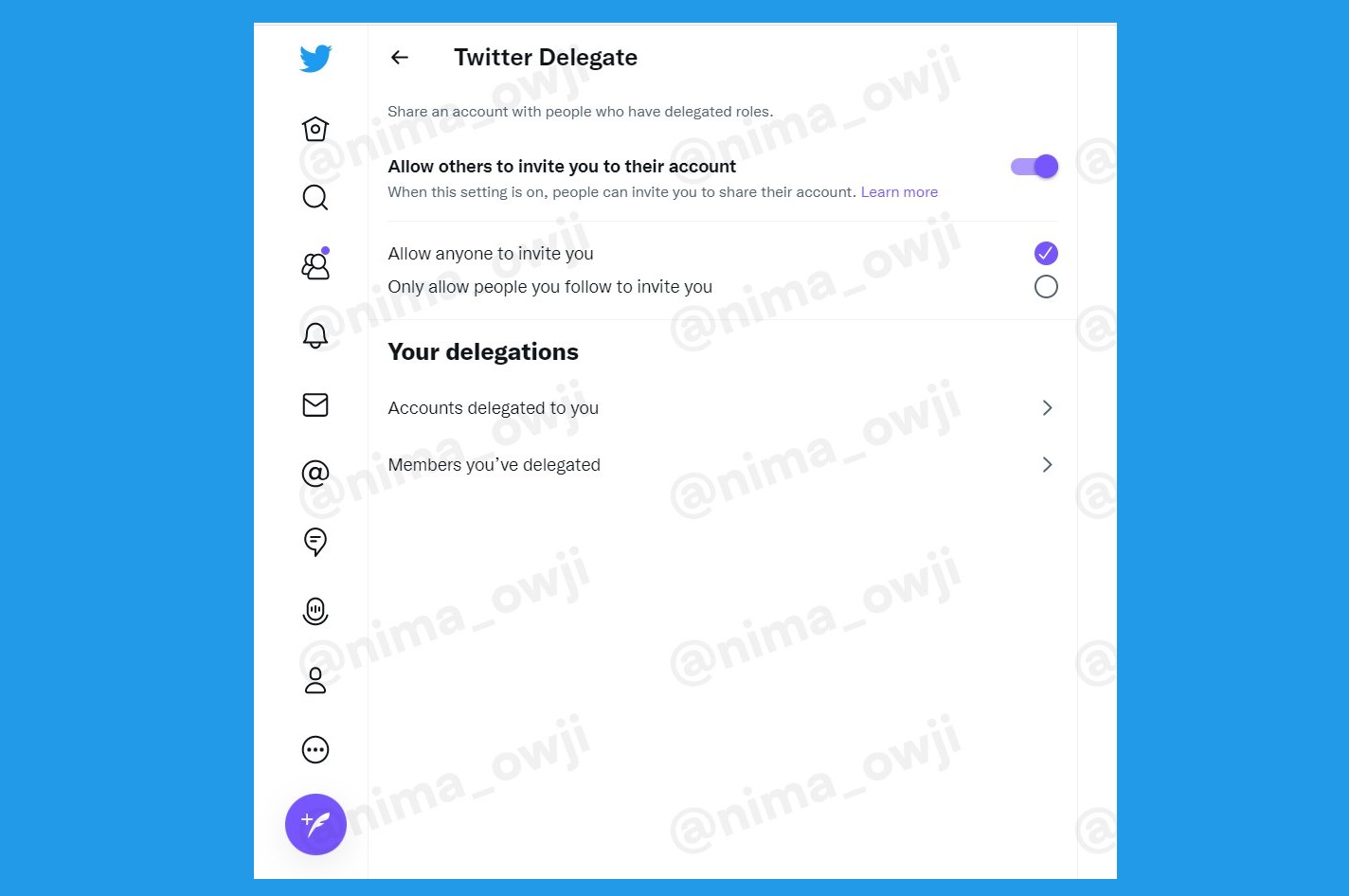
Back in December, a researcher found out that Twitter is working on this new feature and predicted it to launch soon. Six months later, the discoverer, Nima Owji is back with some news. He claims that this time around, the feature has two different sections to it.
The sections are more like user profiles. One is the Contributor while the other is Admin. Both the roles have different powers. A Contributor can send Direct Messages, post Tweets, and lastly, form lists. They can also view all of these activities on the account. It is all the basic things a Twitter user can do.
However, an Admin has more power than that. While the admin can perform all of these tasks, that is sending Direct Messages, publishing Tweets, and making lists, they can also control the Contributors. An Admin's greatest power will be to decide which Contributor to invite or remove. They can also view the account's analytics.
You'll be able to invite someone as a “Contributor” or an “Admin”! pic.twitter.com/14sb2tbB5j
— Nima Owji (@nima_owji) July 26, 2022
What Owji was unable to inform us, or discover, is how Twitter will look once the Delegate feature has been enabled. Since it is a work still under process, we have no way of knowing it. We do suspect that it might look like what Tweet Deck looked like. But we can't be sure until we see any more updates.
Another thing we’re not sure about is how many people will be able to use a Twitter account at once. Once accepted or invited by the Admin a contributor will be able to make tweets however the number of team members is still unknown.
This has been an active year for Twitter and we expect even more new features from the platform. But since most of these new features, and a few of the old ones, have been confined to the US only, we would like to see some regional diversity.
For now, we are impatiently waiting for Twitter Delegate to launch, and we are sure you are too.
Read next: Twitter Launches New ‘Discovery Hashtags’ For Communities That Link Users To Relevant Tweets
by Arooj Ahmed via Digital Information World